Carnegie Mellon Insider Threat Certification
Here are some of the images for Carnegie Mellon Insider Threat Certification that we found in our website database.

Carnegie Mellon University Logo LogoDix

Insider Threat SANCORP

Hiding in Plain Sight: Insider Risk Summit InfraGard Pittsburgh

Global Counter Insider Threat Certification Program Launch GSX
Carnegie Mellon University Logo symbol meaning history PNG brand
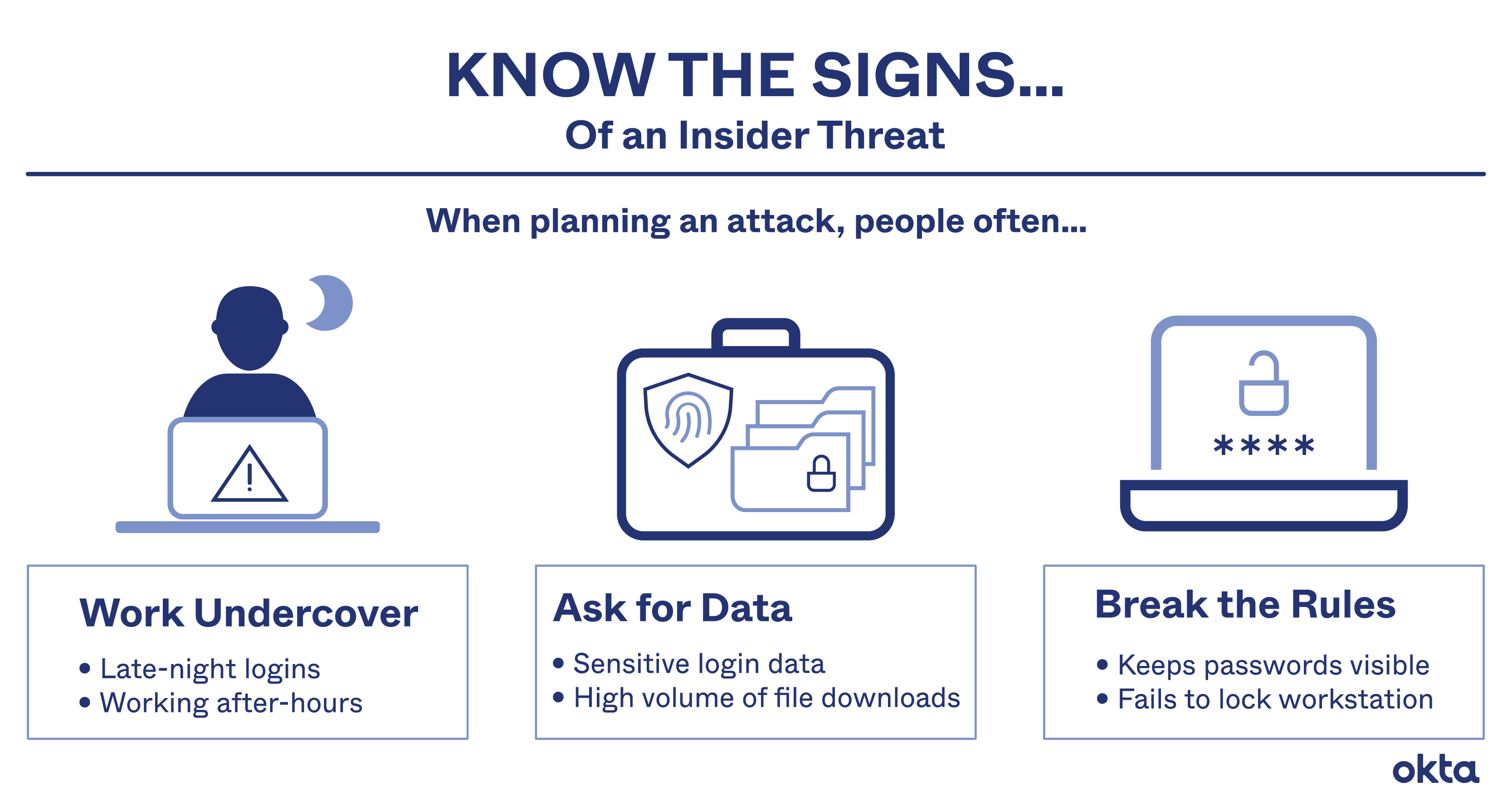
Insider Threat: Definition Prevention Defense Okta

CERT updates insider threat guidebook Help Net Security

CERT updates insider threat guidebook Help Net Security

Reflection on Carnegie Mellon VEX IQ Teacher Certification Progress
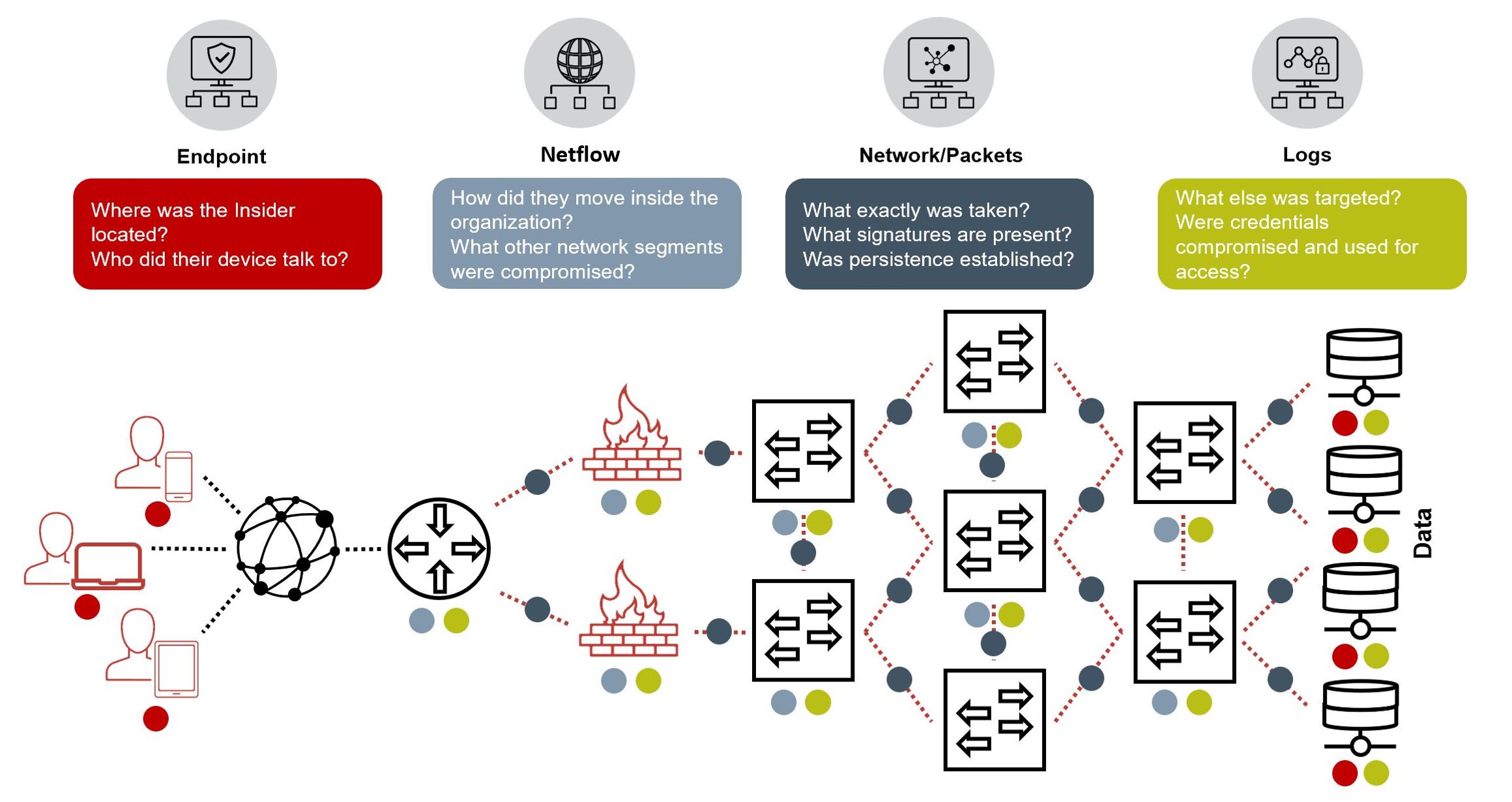
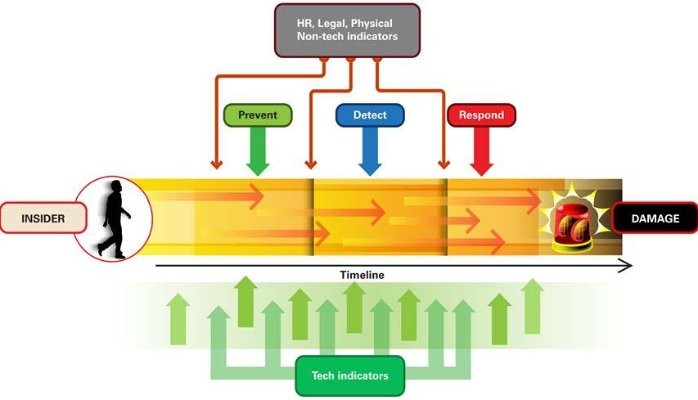
Strategies For Insider Threat Mitigation NetWitness

Dr Anthony J TOLEDO PMD DD ThD CHTI on LinkedIn: New
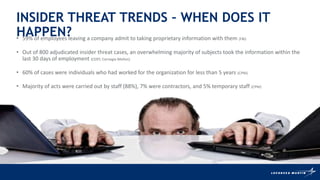
The Insider Threat January pptx
Insider threat what us do d want PDF

Carnegie Mellon student accused of making #39 credible threat #39 : r/pittsburgh

The SEI is holding the NITC Symposium 2020 in support of National
Why your Insider Threat Program should not report to the CISO

The CERT National Insider Threat Center #39 s Dan Costa shares quot Patterns

Teramind on LinkedIn: Insider Threat Detection Course Teramind

CERT Releases Updated Insider Threat Guidebook
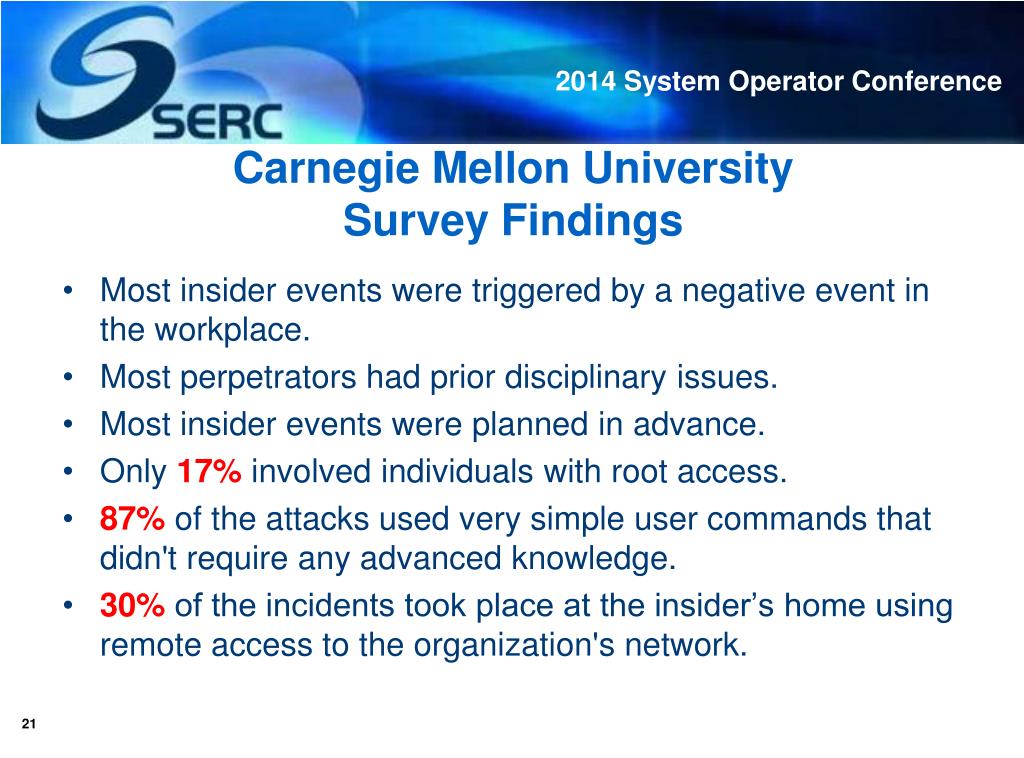
PPT CIP for Operators The Insider Threat PowerPoint Presentation

Teramind on LinkedIn: Insider Threat Detection Course Teramind

Cycle for fraud developed by the Carnegie Mellon Software Engineering
Insider Threat and Information Security Dawn Cappelli Faculty

The Early Indicators Of An Insider Threat Digital Guardian
Software Engineering Institute Carnegie Mellon University on LinkedIn

Insider Threat Prevention in the US Banking System PDF Financial

Insider Threat Prevention in the US Banking System PDF Financial

Carnegie Mellon 202425 Calendar Apple Calendar Tips

The 13 Key Elements of an Insider Threat Program Software Engineering

Example Insider Threat Program Organizational Structure and Data

Carnegie Mellon University

Passed my CERT Insider Threat Program Manager Exam from Carnegie Mellon
Andrew cmu edu Carnegie Mellon University

Malicious Insider Threat CyberHoot
(PDF) Insider threat study: Illicit cyber activity in the information

Most Successful Colleges For Tech Business Insider
Cloud Forensics Certification prntbl concejomunicipaldechinu gov co

Is Your Company Safe From Insider Threats Sentinel Black Gun Safe In

The SEI s version 1 0 of the Insider Incident Data Exchange Standard
OCTAVESM Process 4 Create Threat Profiles PPT
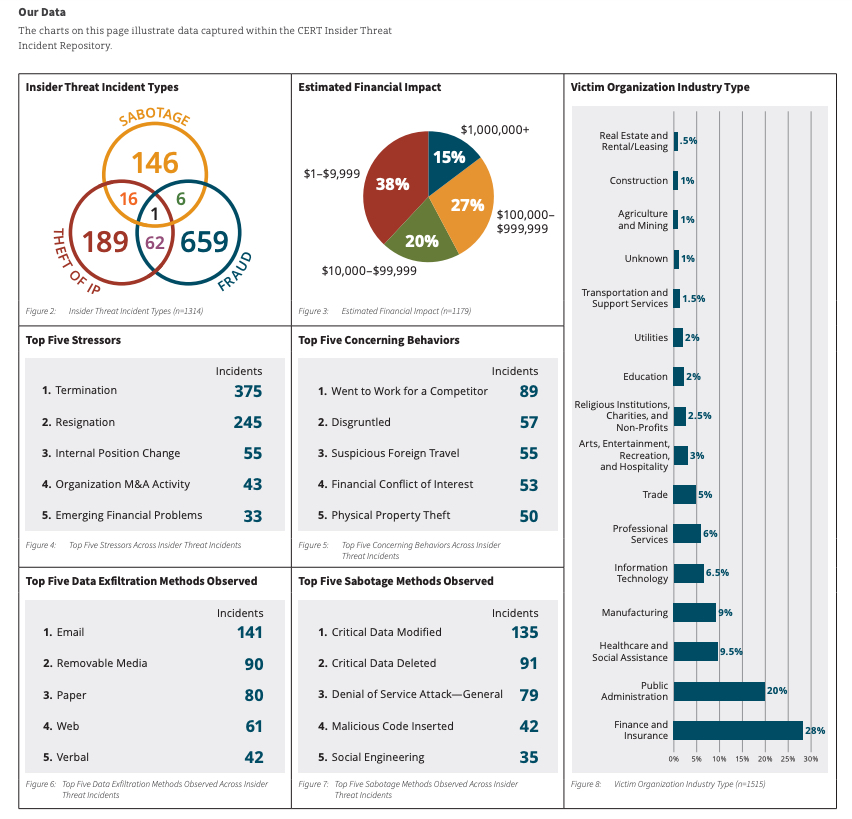
Common Sense Guide to Mitigating Insider Threats ISTARI

Software Engineering Institute Carnegie Mellon University on LinkedIn

Report: Organizations remain vulnerable to increasing insider threats

CERT Releases 2 Tools to Assess Insider Risk Software Engineering

(PDF) Detecting insider threats using Security Information and Event

(PDF) Detecting insider threats using Security Information and Event

How Mature Is Your Insider Threat Program YouTube

Dr Kim Witczak Military Forensic Psychologists

BankInfoSecurity com

Elise Axelrad School of Professional Studies Brown University

Risk Management all about GRC

In a groundbreaking development a team of Carnegie Mellon University

About 1 Au

GitHub hendt5997/capstone: Detection of insider threats using data

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie

HealthcareInfoSecurity com The CERT Insider Threat Center at Carnegie